Spanish engineers find Tinder flaw that reveals users’ location
The error meant that anyone a user ‘matched’ with could see the coordinates of where they were


“Oriol, Tinder is giving me your exact location. I know that you’re in the dining room of your house.” Computer engineer Marc Pratllusá couldn’t hide his surprise when he discovered that the popular dating app was sharing the exact coordinates of fellow security-specialist engineer Oriol Martínez. Pratllusá is a programming expert, but he’s no hacker – and he didn’t need to be to enter Tinder’s servers and access this information. Until this week, a design error in the app allowed someone with minimal computing knowledge to determine the latitude and longitude of each and every one of your “matches.”
We don’t know how long it’s been like this. We can confirm at least three months, but we suspect much longer
The popular dating app offers users various photos of people within the distance they’ve specified, and when both people indicate “like” on each others’ photos, the message “It’s a Match!” appears. After this step, the engineers found that users were able to identify their match’s exact location. The error was active as millions of users connected every day, even if after blocking a user, until this Tuesday when the programmers quietly fixed the glitch without announcing an update or making any other visible changes to the app.
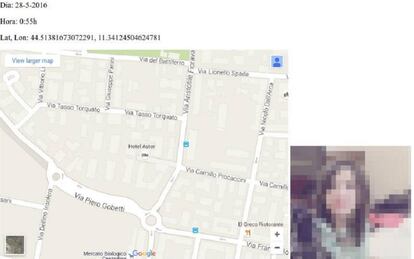
What most worried the Spanish engineers was that the tracking capability was updated each time the user opened the app in a different place. “You had to have moved two kilometers from your previous location in order for the new one to appear,” explains Martínez. When they realized that the coordinates were changing as the hours passed, they decided to conduct a test. Martínez spent a day moving around Barcelona and the surrounding area. He opened the app six times, in six different places. Pratllusá remained in front of the computer; there was no need for him to leave the house. “I was monitoring everything. I knew that at 12.01pm he was leaving Mollet de Vallés and that at 12.21pm he was entering Granollers.”

Tinder has not issued a comment on the design flaw. “The privacy and security of our users is our top priority. We do not discuss specific vulnerabilities that we might find in order to protect them,” the company told EL PAÍS. The answer differs little from what they told the engineers when they brought the glitch to their attention three months ago. “It was an automatic response. ‘Thanks for your feedback.’ Almost three months later, and no change had been made, until we went public with the problem and you all got in contact with them,” they explain.
Martínez and Pratllusá discovered the error almost by accident. In May Pratllusá was working on an application that searched for flights, and he was examining major apps to see how they were built. “We had inspected Facebook, Spotify, Wallapop... and then we tried Tinder,” he says. While studying the design, he realized that it was transmitting unnecessarily precise information. “It’s true that it’s an app that needs to know your location in order to be able to show you new nearby users, but the information should be given in distance, not in coordinates,” described Pratllusá.
To access this information, the engineers only had to install a proxy between Tinder’s servers and the cell phone. This element, which exists in between the two, can read the information being sent to the user’s phone. “Knowing how to place a proxy is simple. Even someone who hasn’t finished an engineering degree can do it. All it takes it having some basic knowledge about how applications and their servers work,” adds Martínez.
When they placed the proxy and saw that something wasn’t functioning correctly, they decided to create a couple of false Tinder profiles to match with other users and confirm that what they were observing on worked with any kind of user. And it did. After they had matched with someone from the app on their cell phone, they could analyze the information and see that person’s exact location. “It seemed like something very serious. We don’t know how long it’s been like this. We can confirm at least three months, but we suspect much longer.”
English version by Allison Light.
Sign up for our newsletter
EL PAÍS English Edition has launched a weekly newsletter. Sign up today to receive a selection of our best stories in your inbox every Saturday morning. For full details about how to subscribe, click here







































